NEXT-GENERATION FIREWALLS

Military-grade AI-powered NGFW for defence applications
The Clavister CyberArmour product family offers state-of-the-art, AI-driven protection tailored for military applications. Designed to secure vehicles and tactical communications, it ensures operational resilience and mission success.
Product highlights

Security by Design
We believe we offer the most robust cybersecurity solutions ever built. We build on 25 years of security track record – the result of a proven secure development lifecycle. The result? Record-few vulnerabilities and unparalleled uptime.
The Swiss Army
Knife of Routing
With incredibly flexible routing capabilities, Clavister CyberArmour is designed to support the most complex network setups.
Application-based Routing
Efficient routing-decisions made by identification of applications. Allow your mission-critical applications to use the best routes available.
Virtual & Dynamic Routing
Deploy multiple virtual routers with powerful policy flows. Dynamic routing protocols ensure interoperability with existing network equipment.
Always-up Philosophy
Through a vast range of health monitors, balancing and fail-over methods, your traffic is guaranteed to reach its destination at all times.
AI-BASED
THREAT DETECTION
Clavister AI capability, the result of years of scientific research, provides instant on-device anomaly detection. Without any cloud dependency, the privacy and confidentiality of your data are preserved.

<15min
ON-DEVICE
TRAINING
No
CLOUD
PROCESSING
Instant
ANOMALY
DETECTION

Military-Grade
design
The products in the Clavister CyberArmour product family are designed to withstand the most harsh conditions. Compliance with MIL-STD-810 and similar standards ensures operational resilience at all times.
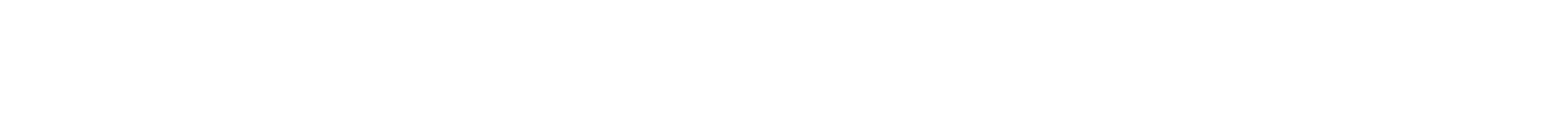
Actionable
security analytics
Clavister CyberArmour integrates seamlessly with Clavister’s powerful security analytics capabilities. A single pane of glass console provides clear, actionable, and comprehensive evaluation of your operation’s cybersecurity readiness. Through a blend of sophisticated algorithms and real-time insights, the system pinpoints vulnerabilities, priorities risks, and offers tailored recommendations to keep your operations secure.
NETWORK SEGMENTATION
A fundamental capability of Clavister CyberArmour is the ability to create proper segmentations of networks.
By restricting access between network segments, the blast radius is significantly reduced in the event of a cyberattack.
CENTRAL MANAGEMENT
AND CONTROL
The Clavister InControl centralised management console provides for easy and efficient management of Clavister CyberArmour products, even for large networks.
Its intuitive interface simplifies administration through features like zero-touch deployment, shared policy sets, and scheduled firmware updates to simplify day-to-day tasks.
With tools for firewall configuration, troubleshooting, firewall backups, and remote access, Clavister InControl is designed to save time and reduce complexity while keeping your network running smoothly.
Through a granular role and permission structure, Clavister InControl integrates well with your security policy framework.

Full
REVISION
CONTROL
Zero
Touch
DEPLOYMENT
Batch
FIRMWARE
UPGRADES

Reliable VPN with
Quantum-resistant
encryption
Clavister CyberArmour delivers reliable and secure site-to-site VPN capabilities, providing encrypted data transmission across networks.
Using the strongest available encryption standards, privacy, integrity and authenticity of sensitive information in transit is maintained at all times.

deep protocol and
application awareness
In-depth recognition, inspection and control of several thousands of protocols and applications allow for the most powerful and granular enforcement of security policies.
selected capabilities
Detect and block stealth communication over common protocols.
Ensure consistent quality-of-service with effective bandwidth management.
Extensive logging for analytics and auditing.
Inspection of, and policies for, granular application attributes.
Apply routing decisions to achieve local internet break-out scenarios.

4,500+
identified applications
and protocols
highly resilient
Network communication in a tactical environment is highly mission-critical. That is why Clavister CyberArmour is built to provide the highest level of resiliency. Through our state-of-the-art high availability capability, seamless switch-over to a secondary device happens within milliseconds, without any interruption of traffic. Extensive health checks, not only on the Clavister CyberArmour product itself but also on links, routes, gateways and even third-party hosts, cater for prompt resolution in case of degradation.

~750 ms
typical fail-over time


quality of service
The advanced quality-of-service capabilities in Clavister CyberArmour ensures optimised bandwidth usage, enabling smoother network performance even during peak loads.
With granular control and intelligent traffic prioritisation, critical communication is secured while maintaining consistent service quality across the full infrastructure.
Complete Communication Hub
The products in the Clavister CyberArmour product family are highly versatile and capable of acting as complete communication hubs in a defence platform or system.
From high-capacity Ethernet switching, through advanced IP routing and full Next-Generation Firewall capabilities, all the way to AI-based threat protection – Clavister CyberArmour can literally assume all roles in a communication network.
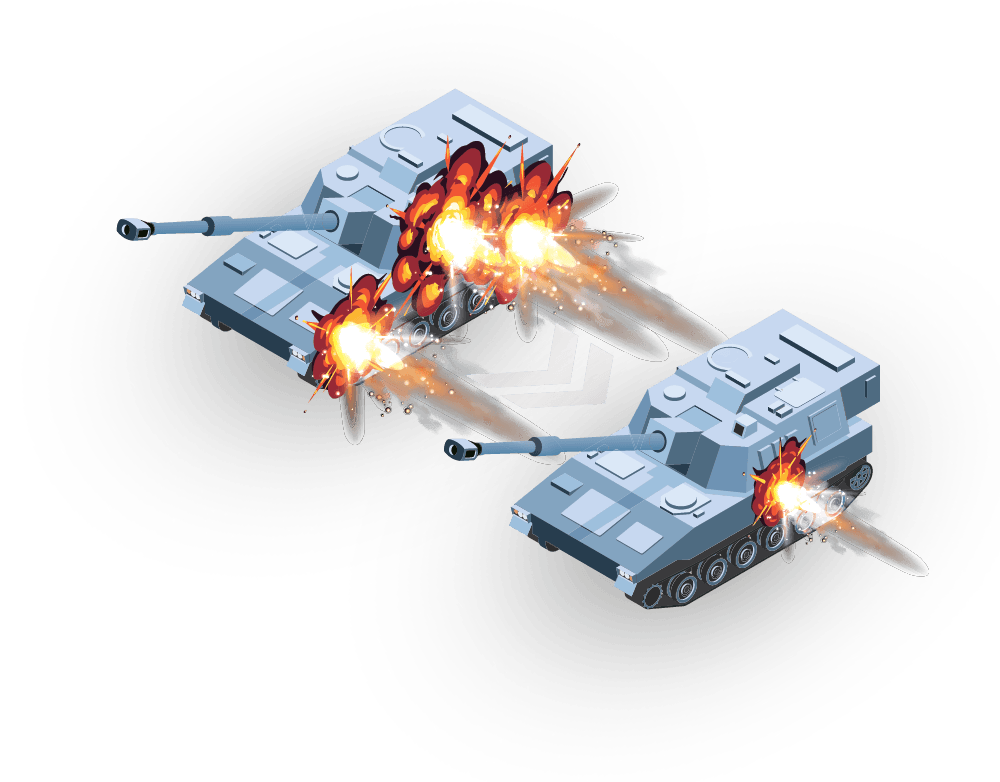
Threat prevention
The Clavister CyberArmour employs a wide array of sophisticated threat prevention capabilities, all seamlessly integrated with each other, working in concert to provide the most efficient mitigation for a vast range of cyberattacks.

Rogue actors can attack systems by infecting components from vendors further down the supply chain. The cyberattack stays dormant until the system is used on the war theatre, exposing the users to lethal risks. Clavister CyberArmour actively
monitors communication and detects and blocks anomalies before they cause an incident.
Defense systems and platforms require strict access control to subsystems and data to prevent unauthorised control or manipulation of high-risk system components. Clavister CyberArmour employs a comprehensive range of segmentation and authentication capabilities to enforce robust access policies effectively.
A DoS cyberattack aims at disrupting the normal functioning of a network by overwhelming it with a flood of malicious traffic. The goal is to make the targeted resource unavailable, causing downtime, inconvenience, and/or financial loss. Clavister CyberArmour reduces the impact of DoS attacks using a combination of mitigation technologies.
Even trusted users can inadvertently introduce malicious content through seemingly harmless activities. Clavister CyberArmour mitigates this risk by restricting communication to a carefully controlled set of subsystems, permitting only safe protocols, applications, and content.
Malware, such as viruses, worms, ransomware and trojans, pose a constant threat to all organisations and can be extremely costly to address once they have gained foothold and begun spreading within a network. Clavister CyberArmour restricts access to websites known for hosting malware, and can furthermore detect malware in transit to reduce the risk of infection.
Hackers commonly abuse poorly written software – both on an application and operating system level – to gain unauthorised access to systems, or to simply cause disruptions. Clavister CyberArmour detects and automatically blocks attempts to exploit known vulnerabilities.
In times of autonomous and remote controlled defence platforms, adversaries gaining unauthorised control poses a significant battlefield threat. Clavister CyberArmour safeguards communication with the strongest encryption standards and ensures access is granted exclusively to legitimate users through multi-layered authentication schemes.
SUPPLY CHAIN ATTACKS

Rogue actors can attack systems by infecting components from vendors further down the supply chain. The cyberattack stays dormant until the system is used on the war theatre, exposing the users to lethal risks.
TactiGate XD actively monitors communication and detects and blocks anomalies before they cause an incident.
unauthorised access
Defense systems and platforms require strict access control to subsystems and data to prevent unauthorised control or manipulation of high-risk system components. TactiGate XD employs a comprehensive range of segmentation and authentication capabilities to enforce robust access policies effectively.
denial-of-services (DoS)

A DoS cyberattack aims at disrupting the normal functioning of a network by overwhelming it with a flood of malicious traffic. The goal is to make the targeted resource unavailable, causing downtime, inconvenience, and/or financial loss. TactiGate XD reduces the impact of DoS attacks using a combination of mitigation technologies.
The human factor

Even trusted users can inadvertently introduce malicious content through seemingly harmless activities. TactiGate XD mitigates this risk by restricting communication to a carefully controlled set of subsystems, permitting only safe protocols, applications, and content.
viruses and other malware

Malware, such as viruses, worms, ransomware and trojans, pose a constant threat to all organisations and can be extremely costly to address once they have gained foothold and begun spreading within a network. TactiGate XD restricts access to websites known for hosting malware, and can furthermore detect malware in transit to reduce the risk of infection.
vulnerabilities and exploits
Hackers commonly abuse poorly written software – both on an application and operating system level – to gain unauthorised access to systems, or to simply cause disruptions. TactiGate XD detects and automatically blocks attempts to exploit known vulnerabilities.
remote hijacking
In times of autonomous and remote controlled defence platforms, adversaries gaining unauthorised control poses a significant battlefield threat. TactiGate XD safeguards communication with the strongest encryption standards and ensures access is granted exclusively to legitimate users through multi-layered authentication schemes.
Products
Products



Contact

Our Experts are Here to Help You
Talk to a Clavister expert today and discover how we can future-proof your security posture.