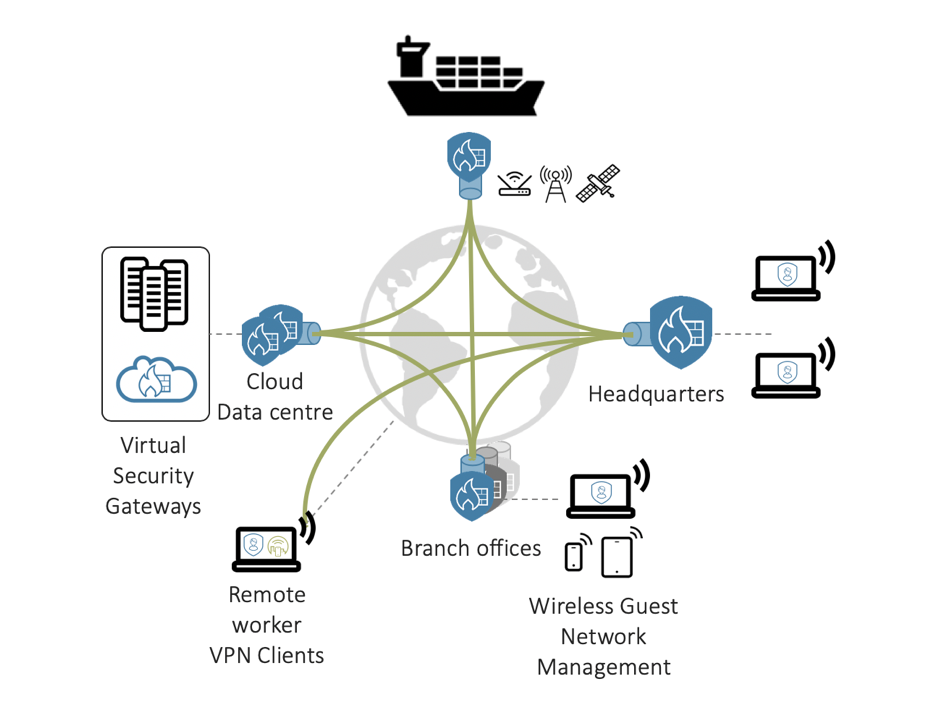
Optimise business connectivity and security across multi-site locations
Setting up a secure wide area network between branch-offices and headquarters, or between headquarters, moving assets such as ships and cloud infrastructure is a heavy administrative job. Virtual Private Network tunnels can be setup between point to point locations and be tuned with different encryption levels and secure protocols. But this is not enough, backup routing needs to be configured, failover and in more complex setups a full mesh connectivity—where each site talks directly to each other site and can route traffic via as well—is optimal.
Even with the tunnel structure configured the network is never static. To be truly adding business value the network must be application aware and prioritize key business services to ensure continuity at the highest level.


SOLUTION
Secure SD-WAN is the answer for IT administrators managing security infrastructure for large multi-site corporations to simplify their deployment and maintenance routines, while saving cost at the same time. No more exclusive MPLS links are needed and any type of access technology can be used in the different locations. Apps are automatically identified as one of the 3000+ detectable services in the Application Visibility & Control use-case, and it’s traffic can thereafter be handled with priority.
With Zero-touch deployment a new branch-office can be deployed and added to the network without ever sending a technician on-site, and traffic management of traffic to the cloud becomes easily manageable from each remote-location directly.
The central management product InCenter is a key component of this solution allowing for a holistic overview and end-to-end approach in one centralized cloud based graphical user interface.
BENEFITS
1
Central management with easy full mesh VPN configuration
2
Application aware routing and network resource usage optimisation
3
Centrally managed perimeter security with local break-out capabilities
Use Cases
The following use cases are included in this solution:
Reliable Secure VPN
Connecting branch offices and remote locations securely and cost effectively
READ MORENetwork Attack Protection
Intrusion detection and prevention system, GeoIP restrictions and denial of service protection
READ MOREApplication Visibility & Control
Control applications and user behaviour to optimize network resource usage
READ MOREProducts
Featured products included in this solution:
Firewall Appliances
Clavister NGFWs, NetWall and NetShield series deliver enhanced network visibility, protection and performance.
Virtual Models
Clavister has been a pioneer in virtual products since 2008. Find out how virtual NGFWs might be the answer for your needs.
NetWall Security Subscriptions
Clavister’s services and knowledge products help you realize the full potential of your newly secured network.