Smart Networks with Edge Computing – How to Achieve Robust Security?

Some datacenter functions are moving closer to the user, to the edge of the networks. Welcome to the world of Edge Cloud Computing—but how does security evolve?
We’re in the midst of an IoT revolution with smart cities, factories and homes that require systems and devices to be connected at all times, producing a massive amount of data that needs processing and needs to render valuable insights in real time. These devices—expected to reach 65 billion devices in the coming years—range from connected light bulbs and other daily items up to connected cars, industrial robotics and even such large, complex systems like a fully automated AI airport control tower. Increasingly, these devices are a fundamental aspect of our lives and they’re requiring an ever-increasing amount of bandwidth and low latency to perform their functions. In a traditional IoT architecture, devices collect data from geographically dispersed sensors and transport this data to a central repository hosted in the cloud, where the data is combined and processed. The resulting insights enable municipalities, enterprises and end users to make better decisions faster and respond to changing conditions in real time.
The majority of IoT devices today are sensors, ones that collect a limited amount of data and thus require low bandwidth usage for transport. These IoT devices are, however, becoming more and more complex, requiring processing of large data feeds, such as real-time video. As an example, security cameras that monitor behavior using artificial intelligence to detect malicious activities require substantial compute resources in the cloud. Another example is digital services such as mobile augmented video services, ones that can help guide tourists visiting a new city by using the camera in their phone to get real-time augmentation on their video feed. Again, something that seems relatively benign requires more network resources than at first glance.
Latency is key
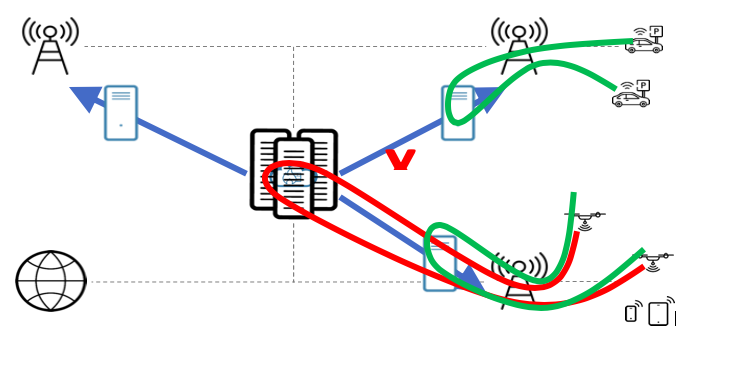
While Cloud Computing has made it possible to process massive amounts of data, it will not be the ideal choice for all applications and use cases. Despite improvements of network technology, datacenters cannot guarantee acceptable transfer rates and response times, which is critical for many of the new services, especially 5G. The solution is to move the processing away from the datacenter to the edge of the network, leveraging physical proximity to the end user. Edge Cloud Computing allows complex processing and analysis of data to be performed with improved response times and reduced bandwidth consumption and energy compared to the traditional cloud computing architectures. At the same time, however, edge computing will introduce new challenges regarding privacy and security.
The distributed nature of edge computing will introduce a shift in the security schemes used in cloud computing. Data must not only be encrypted, but also authenticated at the edge of the network, raising concerns about privacy compared to the centralized top-down infrastructure used in cloud computing moving to a decentralized trust model. To support mobile use cases where the end user is moving around and changing location, the results of the data processing performed at the edge must be synchronized to a central cloud to be distributed to the edge computing location where the user is located. As the raw data is not needed at the central cloud, the transport bandwidth required is significantly reduced compared to a traditional cloud computing architecture where all data must be transported to the cloud.
Security is essential
When devices need to talk to each other in the edge in mesh networks, sometimes using machine-to-machine learning—or data must be processed and reacted upon with ultra-low latency, data transactions will stay in the edge. Security must follow to guard devices and data flows from each other.
Clavister provides virtualized security solutions that provide security software in the edge components requiring minimal resources in terms of memory, CPU and storage, supporting both Intel- and Arm-based architectures. This Services-Based Firewall (SBFW) is dedicated to protecting IoT devices from each other and from cloud resources and is matching perfectly the needs of service providers deploying resource efficient Edge Computing installations, or for deployment into enterprise uCPEs. Combined with the management and integration capabilities of Clavister InCenter will ensure that the infrastructure vital to securing communication between the edge and the central cloud is efficient and resilient, maximizing the benefits of edge computing while maintaining security to protect end user data.
To learn more about Services-Based Firewall (SBFW) and Mobile Edge Computing check out this whitepaper from Heavy Reading here.
Related products:
Clavister NetWall
Clavister NetShield
Clavister InCenter
Terminology:
IoT Internet of Things
SBFW Services-Based Firewall
More reading:








