Empower users with more than MFA

We all know that Two Factor Authentication (2FA) is the foundation of good perimeter security—but it’s often perceived as cumbersome to use. Users want a smooth way to login, it’s why they save passwords in the login dialogues when possible—or choose poor quality, easy to remember variations of passwords. Convenience is, in some ways, the enemy of better security.
When starting a new job an average employee starts with 20 credentials and within three months that number doubles. * Over time the average employee manages nearly 200 logins and passwords—, an incredible amount. Yet this is easy to believe if you add up both personal accounts people have and corporate logins. 91% of users are aware of the risks of reusing passwords, yet 61% continued with the practice. This therefore creates a high-risk scenario for any business. Hackers don’t need to hack-in, they just need to log-in with breached passwords.
Multi Factor Authentication (MFA) provides the opportunity to remove the password dilemma all together. Instead, users must present something they HAVE, together with something they ARE and something they KNOW—for instance a mobile phone, a thumb print and a username. Or a physical USB-key with a unique token, a username and the proof of physical presence. Combinations are endless to suit different organization’s security preferences.

Yet statistics say that only 26% of enterprises of any size have implemented any form of MFA—and it’s hardly ever covering all services. Implementing MFA in an enterprise can be a tough process. Especially since the behavior of every IT user needs to change. Everyone needs to install an app or receive a key, register it and re-learn how to login to their systems. However easy, it takes time. The trick is to change the new login procedure into a positive experience—and this can easily be done with Single-Sign-On (SSO).
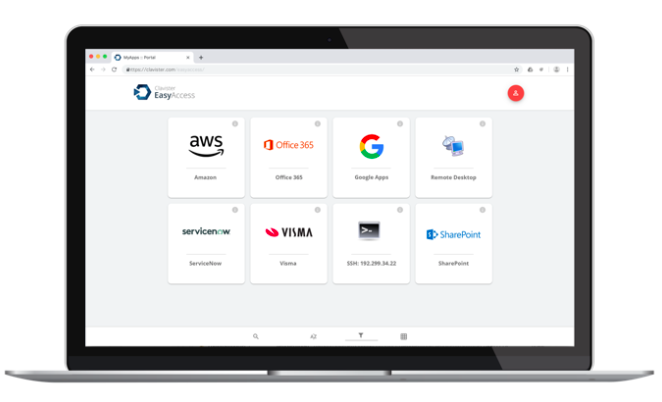
With Clavister EasyAccess, users don’t only get an easy to use biometric way to authenticate themselves quickly and securely with Clavister OneTouch—they also get, when logged in, a personalized Application portal. This portal is rights based, presenting direct links to the applications that are appropriate for that specific user. Applications can be SaaS in the Cloud or on-premises behind the firewall. They can be redirects or reverse proxy based and can even be a remote desktop experience supporting legacy software programs to be presented in the web browser. Applications supporting SAML will receive a passwordless login experience all the way through—making it truly easy for end-users to access data and services.
With access comes great responsibility and IAM solutions of the future must provide tools to handle privileged access management in ways that provides just-in-time access. Think of it as a validation process—where a login request from one person might need to be authenticated– but also require a second person to validate that access is appropriate. Imagine an employee making a money transfer to a third party—after providing approval with biometrics a 2nd push notification goes out to their superior to get biometric validation for the transaction from them as well. Access can be granted to data in the same way—only just-in-time and on a need-to-know basis. Similar with administrator account access. Too many examples exist where it’s the admin account that is poorly protected and being utilized in a cyberattack resulting in major impact quickly. The technology to secure is here today—enterprises just need to decide to use it.
It’s really time to remove the weakest link in security—eliminate the password.
Multi Factor Authentication especially with biometric validation using smart phones are the best way to do this. But IT administrators should not stop there. Implement a personalized portal that helps users with direct access to all their apps, save time and providing a more secure access in the process. Evolve your systems from there to implement Privileged Access Management to control who has access to what at what time—and from what locations.
To read more about Clavister’s Identity Access Management solutions, read here
https://www.clavister.com/products/identity-and-access-management/
By Johan Edlund, CMPO at Clavister
Related products:
ClavisterEasyAccess
Clavister EasyPassword
ClavisterNetWall
ClavisterOneConnect
Terminology:
MSSP Managed Security Service Provider
IAM Identity and Access Management
MFA Multi Factor Authentication
SSO Single Sign On
EPM Enterprise Password Manager
Source:
* DARKReading








